
The TCG Digital Forensics division came to be in the year 2006 when it separated from The Computer Guyz and began offering Digital Forensic services including digital fraud investigations, service of summons, data recovery and CFE in South Africa.
With over 18 years of experience in trading in South Africa, we know exactly where we should be when it comes to our customers market needs as well as the Digital Forensics field. Our incident response team is trained with a broad background of skills ranging from IT intelligence and data investigation to network security and so much more.
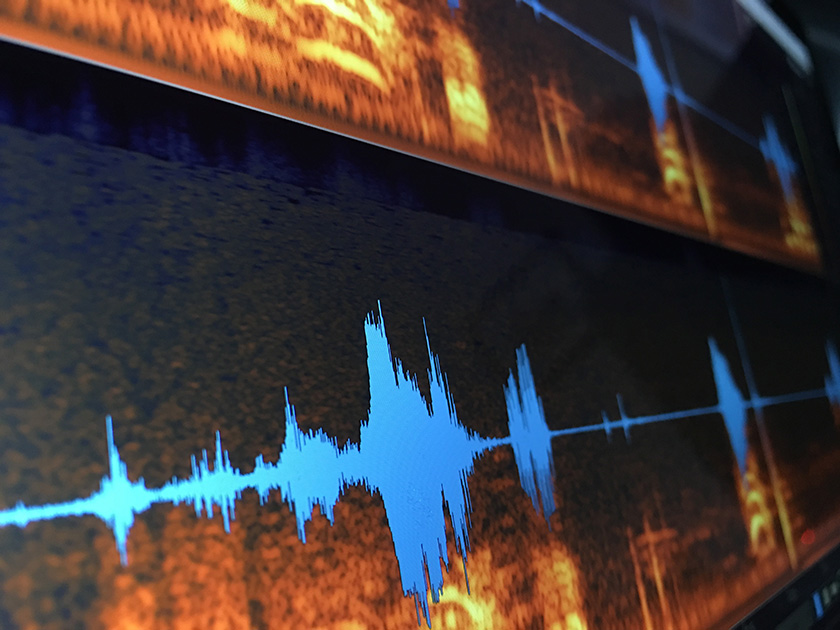
At TCG Digital Forensics, we use the latest software and a system of techniques to collect, research, investigate, and uncover the digital evidence that you require. Our digital forensics services are designed around the requirements of a specific set of clients which includes investigative firms, attorneys, investigators, forensic auditors and blue chip customers, however we do cover a wider scope should you need our assistance.
Do you have a particular set of requirements? Please do not hesitate to contact us at any time. Our main digital forensic investigation offices are in Cape Town, but we do have offices in the Pretoria area and a presence in the coastal area of Durban.
We are proud to offer all our customers clean, professional and methodical digital forensic services supplied by our professional incident response team. Here are some of the Digital Forensic services, including cellular forensics services and computer forensics services that we provide in Cape Town, Pretoria, Durban and nationally…
Incident Response Team
Business Continuity Planning
Cyber Penetration Testing
Hacking Recovery
Cyber Investigations
Cellular Phone Analysis
Hard Disk Drive Analysis
Device Acquisition
Testimony
Due Diligence Investigations
Image Enhancement
Certified Fraud Examiner Services
Service of Summons

Learn more about our Digital Forensics services by visiting our website www.tcgforensics.co.za





:max_bytes(150000):strip_icc()/GettyImages-575504487-5bfef00b4cedfd00263e22d0.jpg)












